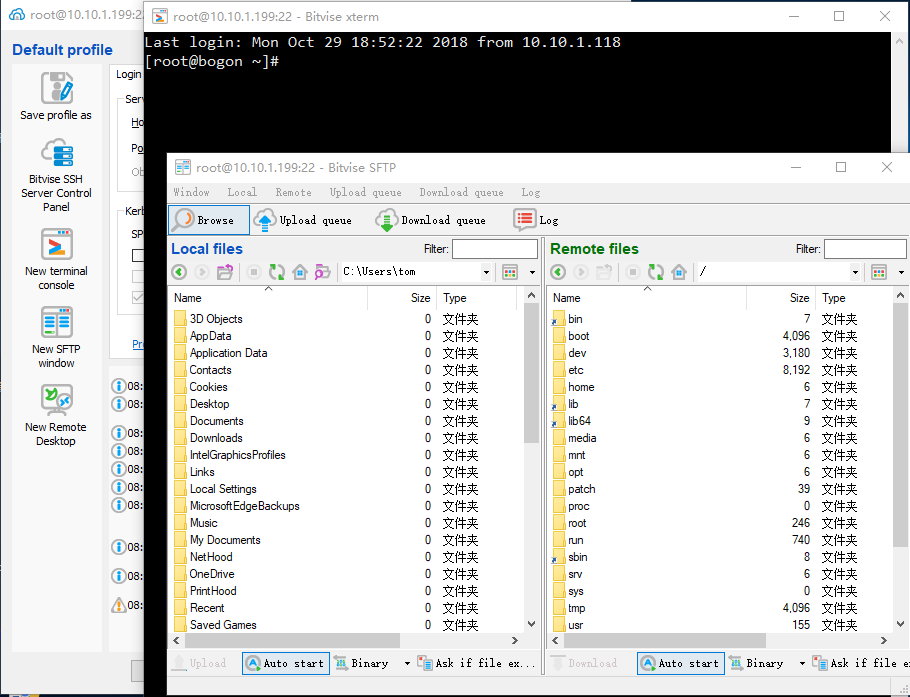
Bitvise SSH 是一款支持 SSH 和 SFTP 的 Windows 客户端。由 Bitvise 开发和提供专业支持。这款 SSH 客户端性能强悍,易于安装、便于使用。Bitvise SSH 客户端拥有功能丰富的图形界面,通过一个有自动重连功能的内置代理进行动态端口转发。Bitvise SSH 客户端对个人用户使用是免费的,同时对于在组织内部的个人商业使用也一样。
如果你的操作系统是 Windows,而你想要连接 Linux 服务器相互传送文件,那么你需要一个简称 SSH 的 Secure Shell 软件。实际上,SSH 是一个网络协议,它允许你通过网络连接到 Linux 和 Unix 服务器。SSH 使用公钥加密来认证远程的计算机。你可以有多种途径使用 SSH,无论是自动连接,还是使用密码认证登录。
Our free and flexible SSH Client for Windows includes state of the art terminal emulation, graphical as well as command-line SFTP support, an FTP-to-SFTP bridge, powerful tunneling features including dynamic port forwarding through integrated proxy, and remote administration for our SSH Server.
You are looking for an SSH client if you wish to initiate connections or file transfers to someone else’s computer. If you are looking to receive connections, you are looking for an SSH server.
Bitvise SSH Client can be used free of charge in environments of any type.
Our SSH client supports all desktop and server versions of Windows, 32-bit and 64-bit, from Windows XP SP3 and Windows Server 2003, up to the most recent – Windows 10 and Windows Server 2016、Windows Server 2019.
Our SSH and SFTP client for Windows incorporates:
- One of the most advanced graphical SFTP clients.
- Single-click Remote Desktop forwarding.
- State-of-the-art terminal emulation with support for the bvterm, xterm, and vt100 protocols.
- Support for corporation-wide single sign-on using SSPI (GSSAPI) Kerberos 5 and NTLM user authentication, as well as Kerberos 5 host authentication.
- Support for ECDSA, RSA and DSA public key authentication with comprehensive user keypair management.
- Encryption and security: Provides state-of-the-art encryption and security measures suitable as part of a standards-compliant solution meeting the requirements of PCI, HIPAA, or FIPS 140-2 validation.
- Obfuscated SSH with an optional keyword. When supported and enabled in both the client and server, obfuscation makes it more difficult for an observer to detect that the protocol being used is SSH.
- Powerful SSH port forwarding capabilities, including dynamic forwarding through integrated SOCKS and HTTP CONNECT proxy.
- Powerful command-line parameters which make the SSH client highly customizable and suitable for use in specific situations and controlled environments.
- An FTP-to-SFTP bridge allowing you to connect to an SFTP server using legacy FTP applications.
- An advanced, scriptable command-line SFTP client, sftpc.
- A scriptable command-line remote execution client, sexec, and a command-line terminal console client, stermc.
- A scriptable command-line tunneling client, stnlc, with support for static port forwarding rules, dynamic SOCKS-based tunneling, and FTP-to-SFTP bridge.
- Our .NET SSH library, FlowSshNet, with example PowerShell scripts showing how to use the SSH library for file transfer and remote program execution from PowerShell.
- Bitvise SSH Server remote administration features.
Changes in Bitvise SSH Client 8.36:
Authors of the Minerva attack have identified a small but significant timing information leak in the Crypto++ implementation of ECDSA over prime field curves. This attack may allow discovery of a private key through repeated observation of signature timing. If the leak can be utilized, an attacker could compromise a server host key or a client authentication key using a practical number of connections across a network.
The following is the impact on Bitvise SSH Server, SSH Client and FlowSsh versions before 8.36:
- On all recent Windows versions (Vista and higher), there is no effect on users of Bitvise software versions 7.xx and 8.xx who use private keys of algorithms RSA, Ed25519, or ECDSA over the NIST curves nistp256, nistp384 or nistp521. On all recent versions of Windows, and using recent Bitvise software versions, these algorithms use Windows cryptography, which is unaffected by Minerva. In the case of Ed25519, we similarly use a non-Crypto++ implementation, which is unaffected.
- On all versions of Windows, using all versions of Bitvise software, the Minerva issue may apply to users who generated, and are using, host keys or client keys of type ECDSA/secp256k1. Bitvise software versions 8.35 and earlier use Crypto++ to implement this algorithm on all platforms. We encourage such users to update to our latest software versions.
- On Windows XP and Windows Server 2003, regardless of Bitvise software version; and for Bitvise software versions 5.xx and 6.xx, regardless of Windows version; the Minerva issue may apply to users of ECDSA private keys of any type. We encourage such users to update to our latest software versions, and/or to update to newer versions of Windows.
With Bitvise SSH Server, SSH Client and FlowSsh 8.36, we are releasing the following mitigations:
- On all recent Windows versions (Vista and higher), where we previously used Crypto++ to support ECDSA/secp256k1, we are switching to alternatives. If the version of Windows is recent enough (for example, Windows 10, Windows Server 2016 and 2019), our default cryptographic provider (CiWinCng) now uses Windows cryptography to support ECDSA/secp256k1 as well as ECDH/secp256k1. Where Windows does not support secp256k1 (for example, Windows Vista to 8.1 and Windows Server 2008 to 2012 R2), we now support it using OpenSSL.
- On Windows XP and Windows Server 2003, we face the issue that maintained cryptographic libraries that continue to support these platforms are hard to switch to and harder to find, while the number of users is small and diminishing. In current versions, we continue to rely on Crypto++ on these platforms, but implement mitigations to make it harder or impossible to observe signature timing across the network.
- On all versions of Windows, we continue to use Crypto++ to support non-standard DSA keys. These are DSA keys as used in SSH of size other than 1024 bits. Since versions 7.xx, we have discouraged the use of DSA keys of any size. Also, DSA is not within scope of the Minerva research, so the current attack does not apply directly. Nevertheless, because we use Crypto++ to support non-standard DSA keys on all platforms, we now activate mitigations for these keys to make it harder or impossible to observe signature timing remotely.
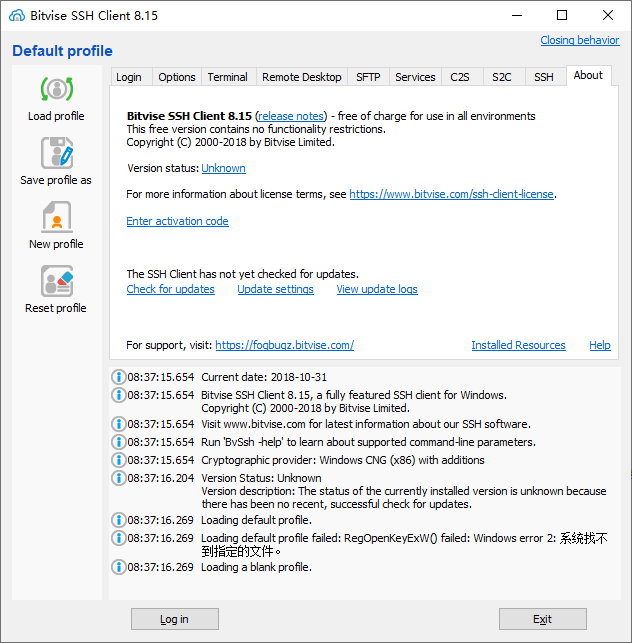
Changes in Bitvise SSH Client 8.15: [ 25 October 2018 ]
Highlights:
- The SSH Client now supports automatic updates. An administrator can configure the SSH Client to automatically apply all updates; only recommended updates; only strongly recommended updates; to apply updates only manually; or to never check for updates.Currently, the SSH Client does not install an update service. It needs to be started from time to time by an administrative user in order to apply updates.
- The graphical SSH Client and sftpc now support recursive directory mirroring. A directory and all of its subdirectories and files can be synchronized either in the upload or download direction. The SSH Client can synchronize updated files and detect and automatically remove files and directories from the target location that are not present in the source.
- The graphical SSH Client and sftpc can now display hashes (cryptographic digests) of local and remote files if the server supports the SFTP v6 check-file extension.
- Bitvise SSH Client and SSH Server now implement automatic host key rotation. The SSH Client will synchronize keys from the SSH Server and any other servers that support the OpenSSH mechanism “hostkey update and rotation”. The SSH Server will announce to clients all configured host keys, including those not employed, to facilitate host key rotation. The SSH Client will automatically trust new keys announced by a trusted server and remove any keys the server has removed, as long as they were added automatically.
- The SSH Client now supports high resolutions and will display crisp text on high-DPI displays such as retina or 4K. The SSH Client now comes with new, higher resolution icons.
- SSH Client profiles downloaded from the internet will now be considered unsafe. If a profile is marked by a browser using which it was downloaded as originating from an unsafe zone, the SSH Client will now load safe parts only. When loading a profile interactively in the graphical SSH Client, a prompt will be displayed, allowing the user to mark the profile as safe. If the user confirms, the profile can be fully loaded.
Cryptography:
- Bitvise SSH Server, SSH Client and FlowSsh once again support non-standard DSA keys larger than 1024 bits. We do not recommend using these keys, and new keys of this type cannot be generated. Also, these keys cannot be used when FIPS mode cryptography is enabled in Windows. Re-adding support for these keys is intended to resolve an obstacle that may still be preventing some users of 6.xx versions from upgrading.
- When using Windows cryptography, Bitvise SSH Server, SSH Client and FlowSsh now implement a backup strategy for DH and ECDH key exchange. Windows implements key exchange, but it does not expose the agreed value in a form suitable for SSH. Bitvise software must retrieve the value by carefully traversing undocumented Windows structures. In versions 7.xx, this required our software to be upgraded to continue working after the Windows 10 1803 update. Our software will now log a warning and fall back to Crypto++ if it cannot perform key exchange because Windows internal structures have changed. However: if FIPS mode is enabled in Windows, this backup strategy is not used, and the software must be updated.
- When importing keys, such as from files, the stage at which an import failed is now described in more detail.
SSH session:
- Bitvise SSH Server and Client now support the elevation extension. In previous versions, if a Windows account with administrative rights connected to the SSH Server, the server would always elevate the session if possible. Otherwise, the user would not be able to get an elevated session because there was no way to convey the user’s preference. With the elevationextension, the user can request a non-administrative security context by requesting no elevation (elevation is still applied by default). In command line clients including stermc, sexec and sftpc, this is controlled using the switch -elevation=n.
- Bitvise SSH Server and Client now support the no-flow-control extension. This disables SSH flow control for clients that only support opening one channel. No flow control is now preferred by sftpc, stermc, sexec and spksc, which only need to open one channel in the SSH session. The graphical SSH Client does not support no-flow-control because it requires multiple channels.
- Bitvise SSH Server and Client now support the ext-auth-info extension. This allows the server to respond to user authentication failures with more detailed information in situations where this is safe. For example, if the client attempts to perform a password change but the new password does not meet complexity requirements, the server can communicate this instead of making the user guess.
- Bitvise SSH Server and Client now support the delay-compression extension. Delayed compression reduces attack surface for unauthenticated clients by delaying availability of compression until after a user is authenticated. The delay-compressionextension is an improvement over previously supported alternatives: the zlib@openssh.com method contains a by-design race condition, while the approach of invoking a second key exchange doubles the overhead of establishing an SSH session.
Terminal:
- Settings for the graphical xterm/vt100 terminal console window (totermw) are now stored in the SSH Client profile instead of in the Windows registry.
SFTP:
- In the graphical SFTP interface, the Open and Edit commands will now be much more responsive if a transfer is already in progress. The in-progress transfer will be paused and the file associated with the Open or Edit command will be transferred as a priority.
- Both the graphical SFTP interface and sftpc can now work with local paths longer than 259 characters, as well as unsafe paths not permitted by Windows in some contexts (e.g. “C:\Com1\file”).
- A new file transfer mode, TextLf, is now supported. This works the same as AutoLf, but forces newline conversions without relying on file type detection.
Tunneling:
- The SSH Client now displays the country (if available) of remote IP addresses. The SSH Client uses the MaxMind GeoLite2 Country database (under license). The country database comes with the SSH Client installation and is not automatically updated, other than by updating the SSH Client itself.
Command line clients:
- It is now easier to connect to SSH servers that accept connections on non-default ports. If no port is specified on the command line, but the SSH Client knows a host key for the destination server, the SSH Client will automatically connect to the port associated with the server in the host key database. If there are multiple port associations, however, the port still needs to be specified, unless one of them is 22.
- It is now easier to enable and disable individual algorithms with our command-line clients. Previously, to use non-default algorithms, either a -profile needed to be used, or a complete algorithm list had to be supplied using -hkey, -kex, -encr or -mac. It is now still possible to pass a whole list using the same parameters, or using their new aliases -hkeyAlgs, -kexAlgs, -encrAlgs or -macAlgs. In addition, it is possible to modify the default algorithm lists using -hkeyMod, -kexMod, -encrMod or -macMod. When using the “Mod” versions, provide a comma-separated list of algorithm names with optional prefixes. Names prefixed with “+” are added to the front of the list; names without a prefix are appended to the end; and names prefixed with “!” are removed. Example: -encrMod=+aes256-gcm,!3des-ctr
Utilities:
- The log utility now supports filesystem paths in Unicode.
Known issues
- LastPass for Applications achieves some of its functions by injecting a DLL with foreign code into other applications. As of February 2018, the DLL injected by LastPass has been observed to cause a crash in Bitvise SSH Client when connecting to a server.
- Windows XP: All versions of our software that we recommend using are built using Visual Studio 2015. The C++ run-time library used by this Visual Studio version has a known issue where 1-2 kB of memory are leaked each time a new thread is created. This issue does not occur on later Windows versions; it does not occur e.g. on Windows Server 2003. Microsoft has stated they do not intend to fix this issue. Bitvise’s view is that the impacts on our SSH Client and FlowSsh are manageable; whereas our SSH Server is rarely used on Windows XP. We therefore do not plan to work around this; but we warn that this can be a potential denial of service vector on Windows XP.
软件下载地址:
Bitvise SSH Client v8.36
Download 城通网盘:https://545c.com/file/3477565-404643114
Download 城通网盘:https://t00y.com/file/18818253-404643173
Download 百度网盘:https://pan.baidu.com/s/1ljjgtQwEJ6iLdumZDdhieQ 密码:gdn5
Bitvise SSH Client v8.15
Download YunFile云盘:http://yfdisk.com/fs/etop2molcd18b2a8/
Download 皮皮网盘:https://sun0816.pipipan.com/fs/3477565-317229939
Download 城通网盘:https://sun0816.ctfile.com/fs/3477565-317229939
Download 百度网盘:https://pan.baidu.com/s/1hfZA1Ar2nRQT1HA5Tzz97A 密码:k57u
解压密码:www.unyoo.com
 联合优网
联合优网